Category: Geopolitics

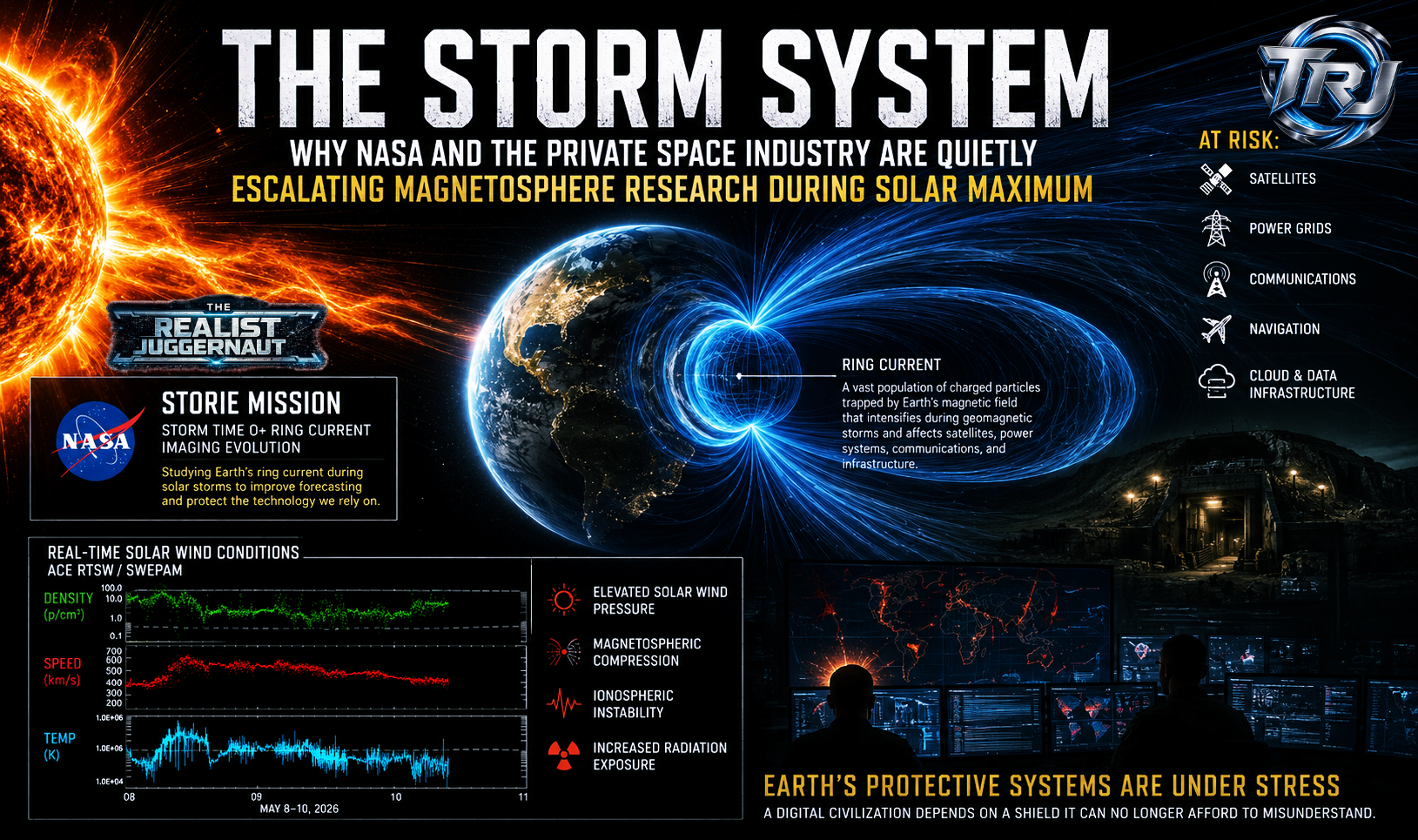
THE STORM SYSTEM: Why NASA and the Private Space Industry Are Quietly Escalating Magnetosphere Research During Solar Maximum

Ransomware Suspect Identified in Prior TRJ Investigation Released in Russia–France Prisoner Exchange

Russia Orders Apple to Prioritize Domestic Search Engines — Moscow Tightens Grip on Digital Sovereignty
THE STRIKE BEFORE THE LEAK: Why President Trump Didn’t Need Congressional Approval to Bomb Iran’s Nuclear Sites

INFILTRATION ALERT: Chinese State-Backed Hackers Target Taiwan’s Critical Infrastructure — Long-Term Espionage Campaign Exposed

Taiwan’s Critical Infrastructure Targeted by Suspected Volt Typhoon-Linked HackersBy The Realist Juggernaut
The Illuminati, New World Order, and the Modern Power Structures: An In-Depth Analysis of Global Control